AWS Cloud Foundations
Move Beyond Ad-Hoc AWS to Governed Enterprise Cloud
550+ Engagements Since 2006 — Trusted By
AWS debt rarely surfaces until the damage is already compounding. It builds through permissive roles, accounts provisioned outside any formal process, and a network topology that expanded until no single person understood it. The reckoning usually arrives as a failed audit or a breach that properly structured foundations would have stopped. Our AWS Cloud Foundations service exists to close that gap. We begin by mapping where your account hierarchy and access controls are exposing workloads to risk, then replace them with structured, auditable foundations your teams can operate confidently within.
CUSTOMER STORIES
Client Results and Success
WHAT WE DO
Our AWS Cloud Foundations Services
Account Structure & Landing Zone Design
IAM & Access Governance
Security Scanning & Compliance Automation

WHAT WE DO
Complete Backend Engineering Services for Enterprises and Companies
Product Backend Studio
Enterprise Backend
Cloud & Platform Engineering
Data & Infrastructure Engineering
OUR RANGE OF IMPACT
Industries-Based AWS Cloud Foundations
THE GEEKYANTS DIFFERENCE
AWS Cloud Foundations by Engineers Who Have Delivered 1000+ Projects
FEATURED CONTENT
Our Latest Thinking in Backend Engineering

Nov 28, 2024
Revolutionizing Home Waxing: An Application Tailored for Convenience and Expertise
Revolutionize home waxing with GeekyAnts' app! Enjoy salon-grade products, expert tutorials, community support, and rewards—making grooming seamless, professional, and empowering.
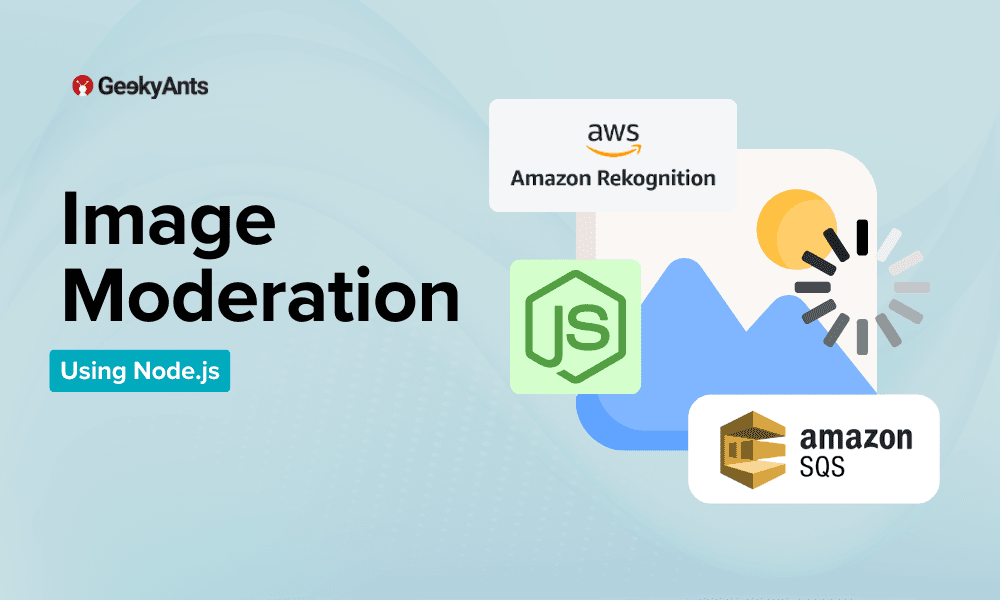
Aug 5, 2024
Image Moderation Using Node.js, Amazon Rekognition and SQS
Implement image moderation with Node.js, Amazon Rekognition, and SQS. This guide details setting up an automated system for content analysis and moderation.

Jul 19, 2024
The Importance of BFF in Frontend Development
BFF (Backend for Frontend) enhances frontend performance by optimizing data retrieval and formatting. It simplifies development, reduces browser load, and improves user experience.

Jun 24, 2024
AWS WAF - Protect Your Web Applications From Common Exploits
Explore how AWS WAF helps you protect your web applications against common web exploits and bots that can affect availability, compromise security, or consume excessive resources.
Jan 10, 2023
New Tech Stacks Added To Our Profile In 2022, And Plans For 2023
Here's a look at the new technologies GeekyAnts added to its front-end and back-end stacks in 2022 and plans to add in 2023.

Sep 3, 2021
A Comprehensive Guide To Backend Tech
An introduction to the Backend, its significance to Fullstack development and much much more...
Build with us.Accelerate your Growth.
Customized solutions and strategiesFaster-than-market project deliveryEnd-to-end digital transformation services
Trusted By
Book a Discovery Call
Build with us.Accelerate your Growth.
- Customized solutions and strategies
- Faster-than-market project delivery
- End-to-end digital transformation services
Trusted By

What You Need to Know