Security should not slow users down.
Identity & Access Management
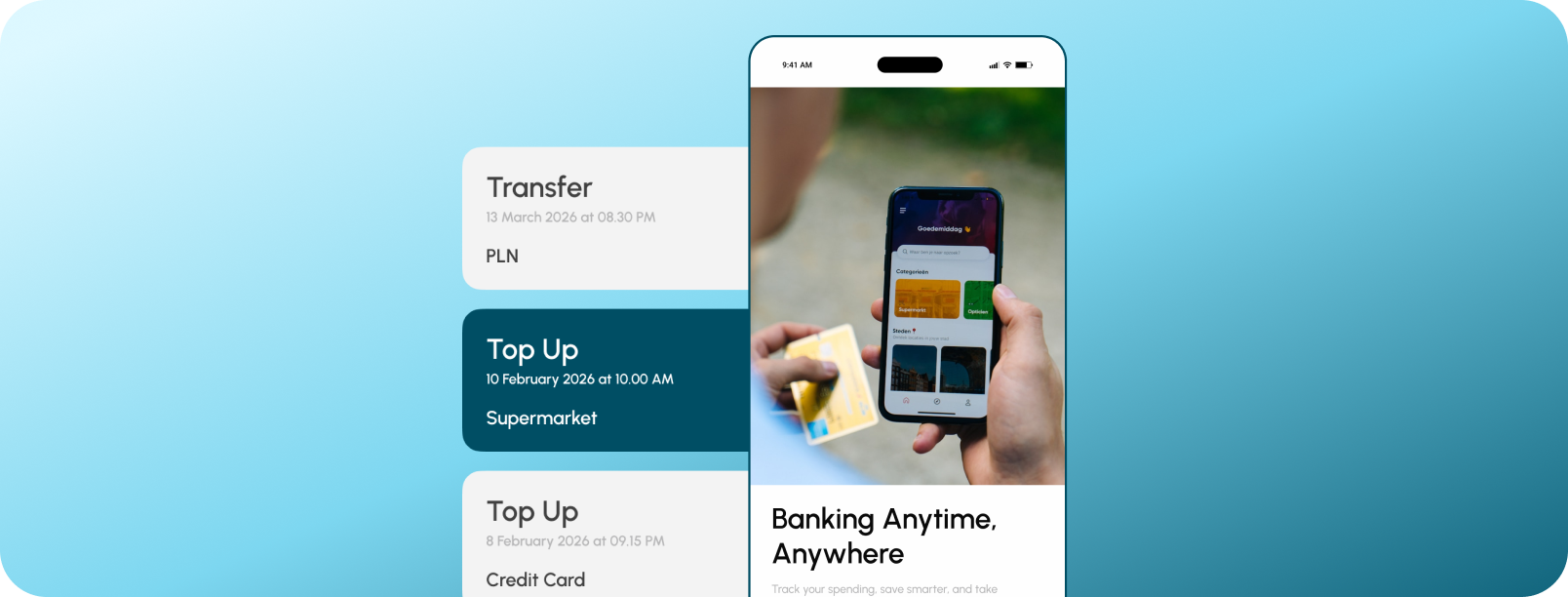
We build banking-grade login systems that go beyond simple passwords. By using SIM binding and carrier API integration, the app automatically verifies the user's phone number in the background.

Security should not slow users down.
550+ Engagements Since 2006 — Trusted By
Traditional 2FA is now a liability; hackers easily intercept SMS codes via SIM swapping, and high messaging fees drain your budget.
CUSTOMER STORIES
Client Results and Success
RESULTS DELIVERED
Business Impacts We Have Made
OUR SERVICES
Our Identity & Access Management Capabilities
SIM Swap Detection via Carrier APIs
Device and SIM Binding for Banking Apps
Silent Authentication via MNO APIs
Local SMS Gateway 2FA
IoT Device Authentication Support
Multi-Factor Authentication Orchestration
OUR OFFERINGS
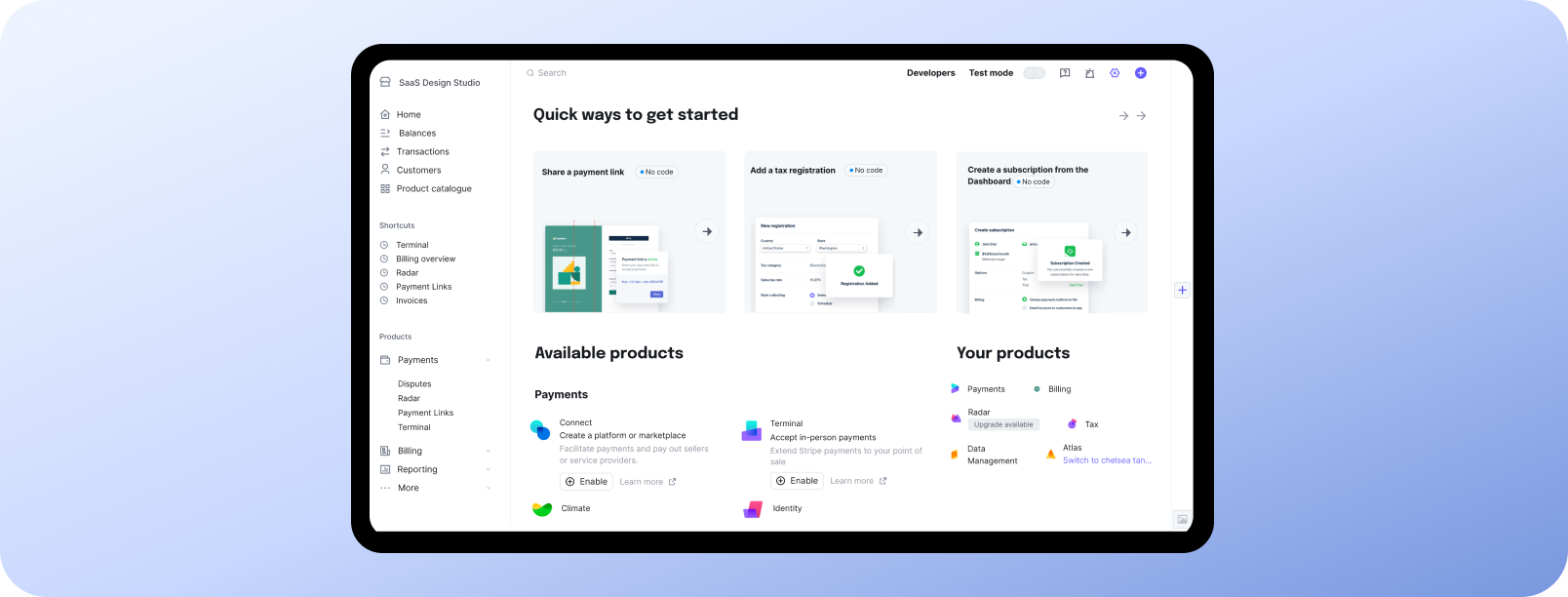
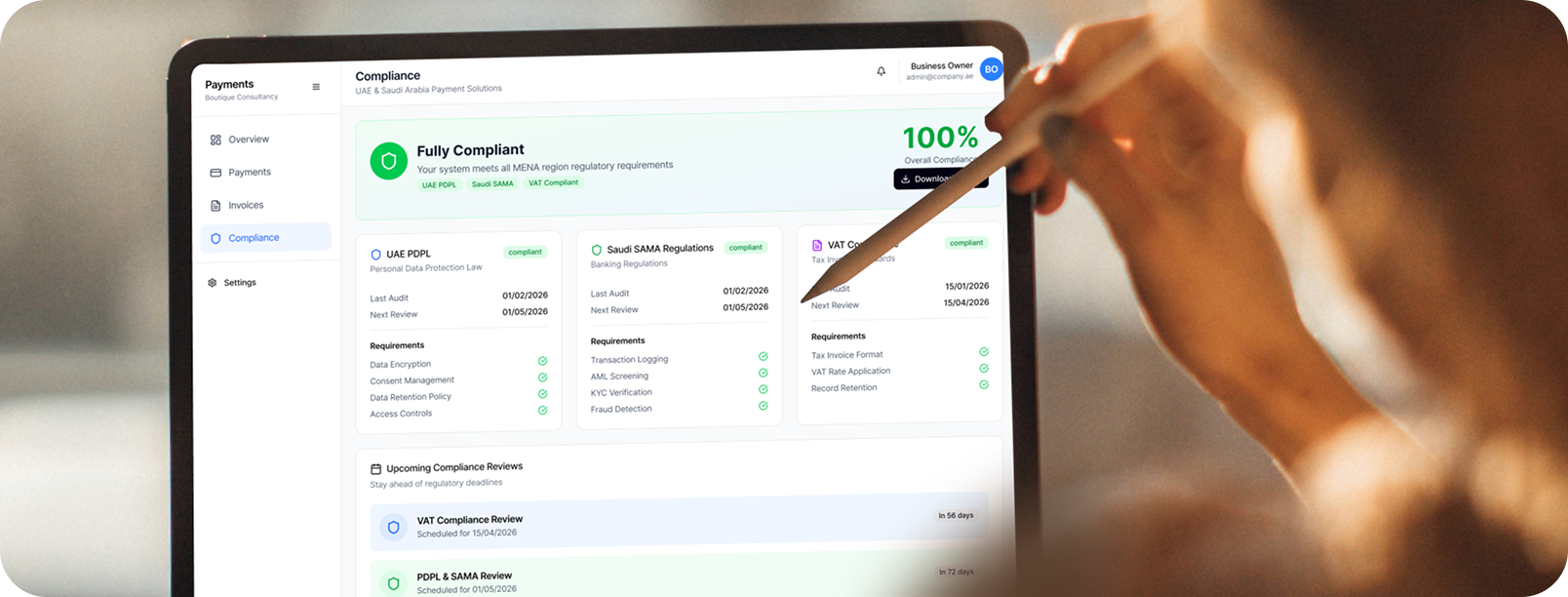
Complete RegTech & Compliance Automation Solutions for Financial Enterprises
KYC and AML Automation
Application Security (RASP)
Identity and Access Management
Fraud Detection and Monitoring
Regulatory Reporting & Compliance
TECHNICAL HIGHLIGHTS
Identity & Access Management by Engineers and Consultants Who Have Delivered 1000+ Projects
Direct Carrier Connections (MNO Integration)
Modern iOS Security (Post-API Deprecation)
Direct SMS Routing (SMPP Protocol)

Featured content
Our Latest Thinking in RegTech & Compliance Automation

Apr 23, 2026
From Manual Testing to AI-Assisted Automation with Playwright Agents
This blog discusses the value of Playwright Agents in automating workflows. It provides a detailed description of setting up the system, as well as a breakdown of the Playwright Agent’s automation process.

Apr 14, 2026
The Keyboard Bounce of Death: Handling Inputs on Complex React Native Screens
Fix the React Native ‘Keyboard Bounce of Death.’ Learn why inputs jump and how to build smooth, production-ready forms with modern architecture.

Apr 9, 2026
From RFPs to Revenue: How We Built an AI Agent Team That Writes Technical Proposals in 60 Seconds
GeekyAnts built DealRoom.ai — four AI agents that turn RFPs into accurate technical proposals in 60 seconds, with real-time cost breakdowns and scope maps.

Apr 6, 2026
How We Built an AI System That Automates Senior Solution Architect Workflows
Discover how we built a 4-agent AI co-pilot that converts complex RFPs into draft technical proposals in 15 minutes — with built-in conflict detection, assumption surfacing, and confidence scoring.

Apr 6, 2026
AI Code Healer for Fixing Broken CI/CD Builds Fast
A deep dive into how GeekyAnts built an AI-powered Code Healer that analyzes CI/CD failures, summarizes logs, and generates code-level fixes to keep development moving.

Apr 2, 2026
A Real-Time AI Fraud Decision Engine Under 50ms
A deep dive into how GeekyAnts built a real-time AI fraud detection system that evaluates transactions in milliseconds using a hybrid multi-agent approach.
Build with us.Accelerate your Growth.
Customized solutions and strategiesFaster-than-market project deliveryEnd-to-end digital transformation services
Trusted By
Book a Discovery Call
Build with us.Accelerate your Growth.
- Customized solutions and strategies
- Faster-than-market project delivery
- End-to-end digital transformation services
Trusted By

What You Need to Know