01
Secure & Scalable Foundations
Code Quality & Engineering Excellence
We provide engineering audits, security hardening, and architectural remediation to ensure your foundation supports rapid, secure scaling. We identify the risks that automated tools miss.
550+ Engagements Since 2006 — Trusted By
CRITICAL RISK INDICATORS
Patterns of Engineering Fragility
If your system exhibits these patterns, your engineering foundation is a primary business risk.
Deployment Latency
Manual release processes or fragile pipelines that turn deployments into high-risk events.
Zero Test Coverage
Lack of automated test coverage leading to consistent fix-one-break-two scenarios.
Security Exposure
Hardcoded secrets, missing input validation, or OWASP vulnerabilities await discovery.
No Code Review Process
Absence of code review gates and PR oversight, allowing the codebase to grow without structural cohesion.
Documentation Doesn’t Exist
Minimal documentation and a lack of architecture diagrams make engineer onboarding slow and error-prone.
Production Is a Black Box
No proactive monitoring or error tracking. Incidents are reported by users rather than system alerts.
AUDIT SCOPE
A 6-Dimensional Technical Assessment
We evaluate your foundation across sixty critical checkpoints, providing a severity-rated remediation roadmap for every finding.
Code Architecture
- Project structure and modularity
- Design patterns and consistency
- Separation of concerns
- API design and contracts
- Database schema and relationships
- Error handling patterns
Security Assessment
- OWASP Top 10 vulnerability scan
- Authentication and authorization review
- Secrets management audit
- Input validation and sanitization
- Dependency vulnerability analysis
- Network and infrastructure security
Testing & Quality
- Test coverage analysis
- Test quality and effectiveness
- CI/CD pipeline evaluation
- Code review process assessment
- Linting and formatting standards
- Type safety and static analysis
Performance
- Frontend performance (Core Web Vitals)
- API response time profiling
- Database query optimization
- Bundle size and loading strategy
- Caching implementation
- Memory and resource utilization
Infrastructure & DevOps
- Cloud architecture review
- Deployment pipeline analysis
- Environment configuration
- Monitoring and alerting setup
- Backup and disaster recovery
- Cost optimization opportunities
Developer Experience
- Onboarding documentation
- Local development setup
- Code contribution workflow
- API documentation quality
- Debugging and troubleshooting tools
- Technical debt inventory
Get a Clear Engineering Risk Report
We analyze 60 critical technical checkpoints and deliver a prioritized remediation roadmap.
Schedule Your Technical Assessment
RED FLAGS WE FIND
Signs Your Codebase Is A Business Risk
If three or more of these patterns sound familiar, your engineering foundation is likely costing you more than it is worth.
Release Anxiety
Deployments take hours and feel like a gamble. Without an automated pipeline, your team fears "Release Day" instead of using it to grow.
The Bug Cycle
One fix creates two new problems. Without automated testing, you are constantly fighting the same errors instead of building new features.
Security Gaps
From hardcoded keys to missing login checks, your data is one simple mistake away from a public breach.
Invisible Progress
Code is merged without review or oversight. Without a clear review process, your product's architecture becomes a tangled mess that no one fully understands.
Knowledge Silos
There is no documentation. Onboarding a new hire takes weeks because all the system knowledge is trapped in one person’s head.
Silent Failures
You learn about crashes from angry customers, not your own systems. Without monitoring, your production environment is a black box.
OUR ENGINEERING STANDARDS
The Bar We Hold Every Project To
> 80% Automated Test Coverage
< 5 Minutes Deployment Speed
< 2 Minutes Rollback Time
0 Critical Issues
100% Reviewed Peer Oversight
< 30 Seconds Alert Response
THE STRATEGIC AUDIT PROCESS
Audit Complete in 2 – 3 Weeks.
Fast enough to inform your next fundraiser. Thorough enough to catch the issues that matter. Every finding comes with a specific, actionable recommendation.
02
Automated Quantitative Foundation
03
Senior Architect Manual Review
04
Prioritized Remediation Roadmap
Know What Your Codebase Is Really Costing You
Schedule a discovery call with our engineering team to understand the gaps, the risks, and the fastest path to stabilizing your codebase.
LET’S TALK
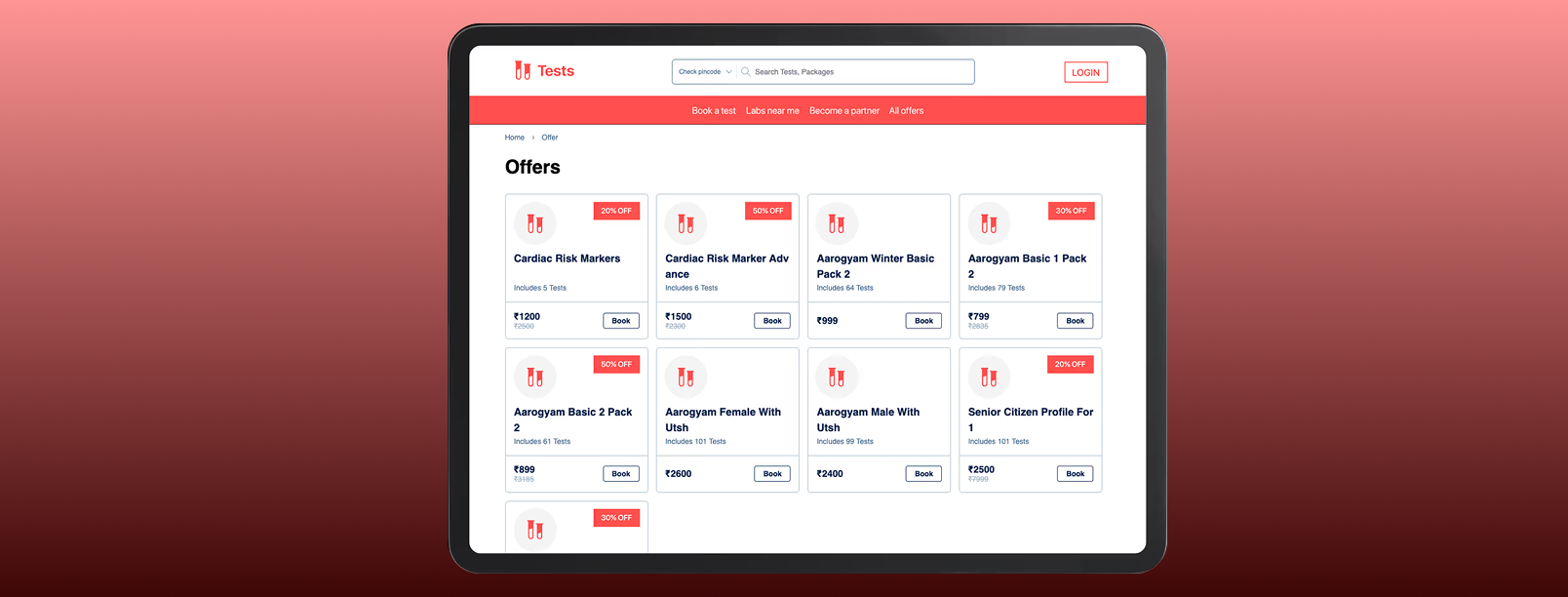
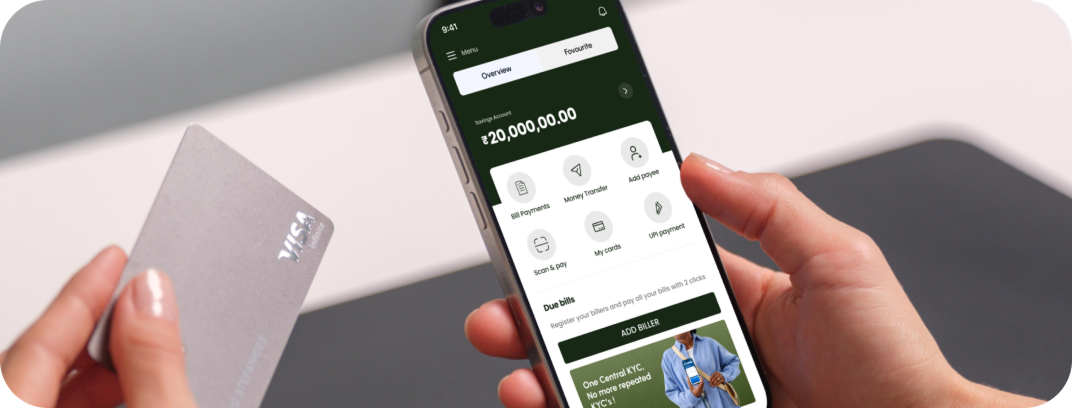
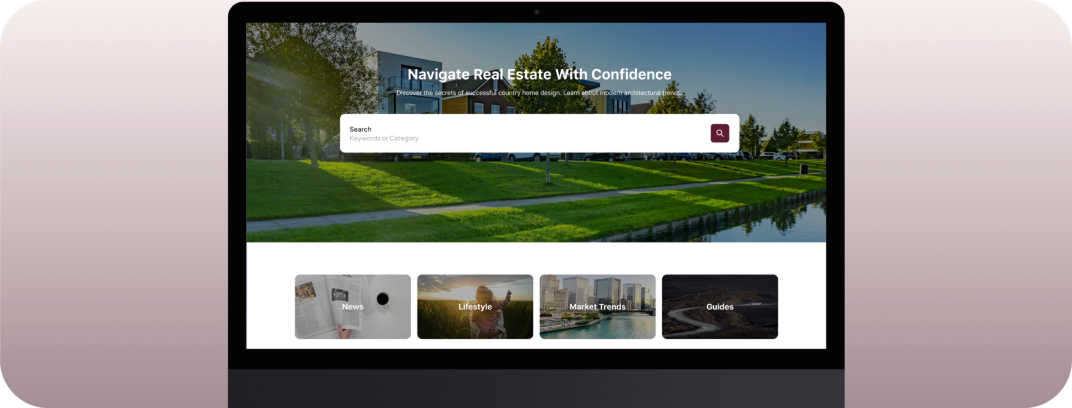
CUSTOMER STORIES
Impact We Have Made
EXPLORE OUR CAPABILITIES
More Ways We Can Help You with AI-Powered Product Engineering
Prototype to Production
In 6-8 Weeks
AI-Native Engineering
Architecture Ready in 2 Weeks
Fractional Engineering Team
1-10 Skilled Engineers in 2 Weeks
Code Quality and Engineering Excellence
Code Audit in 2 Weeks
Scaling MVP to Market Leader
Market-ready App in 3-4 Months
Product Studio for the AI Era
Custom Sprint
Your Codebase Is A Liability
Schedule an engineering audit to identify the technical risks stalling your next funding round.
TRUSTED BY
Book a Discovery Call
Your Codebase Is A Liability
Schedule an engineering audit to identify the technical risks stalling your next funding round.
TRUSTED BY







FEATURED CONTENT
Our Latest Thinking in AI-Powered Product Engineering
Discover the latest blogs on Our Latest Thinking in AI-Powered Product Engineering, covering trends, strategies, and real-world case studies.

May 7, 2026
The AI native Enterprise Evolution | Saurabh Sahu
Explore Saurabh Sahu’s insights on AI-native enterprise, AI gateways, model governance, agentic SDLC, and workspace.build for scalable AI adoption from thegeekconf mini 2026.

May 6, 2026
Scaling AI Products: What Leaders Must Validate Before the Big Push
AI pilots are over. Learn what leaders must validate before scaling AI products for real business impact, trust, compliance, and profitability.

May 6, 2026
Why Security Readiness is the Ultimate Revenue Gatekeeper for AI
Discover why security readiness is the real revenue gatekeeper for AI, helping firms close deals faster, reduce churn, and win enterprise trust.

May 5, 2026
The Next Era of AI Builders: Building Autonomous Systems for Frontier Firms — Pallavi Lokesh Shetty
Discover Pallavi Shetty’s view on the next era of AI builders, covering autonomous systems, trusted agents, data quality, and frontier firms from thegeekconf mini 2026

May 5, 2026
The Autonomous Factory: Architecting Agentic Workflows with Clean Code Guards | Akash Kamerkar
Akash Kamerkar’s thegeekconf mini 2026 talk explores the ACDC framework for building safer agentic workflows with clean code guards, sandbox testing, and AI-driven software development.

May 4, 2026
OpenClaw: Build Your Autonomous Assistant | Deepak Chawla
Discover how Deepak Chawla explains OpenClaw for building autonomous AI assistants through data preparation, knowledge bases, AI engines, and agent automation.
What You Need to Know