Fragmented Data Creates Compliance Gaps
Application Security (RASP)
We implement Runtime Application Self-Protection for banking applications, detecting and responding to threats from within the application layer itself.

Fragmented Data Creates Compliance Gaps
550+ Engagements Since 2006 — Trusted By
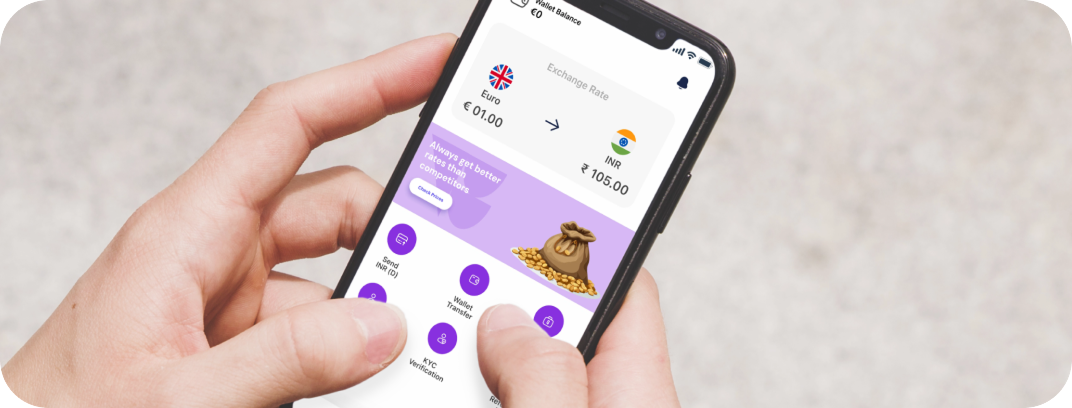
Firewalls only guard the front door of your servers. But if a customer’s phone is infected with malware or a spy app that records their screen, the hacker can see everything. Most apps are blind to this.
CUSTOMER STORIES
Client Results and Success
RESULTS DELIVERED
Business Impacts We Have Made
OUR SERVICES
Our Application Security (RASP) Capabilities
RASP & Security
Device Integrity
Reverse Engineering Fix
Screen & Privacy Locks
SIM Swap Protection
Safe Crash Analytics
Backend Compliance Logging
OUR OFFERINGS
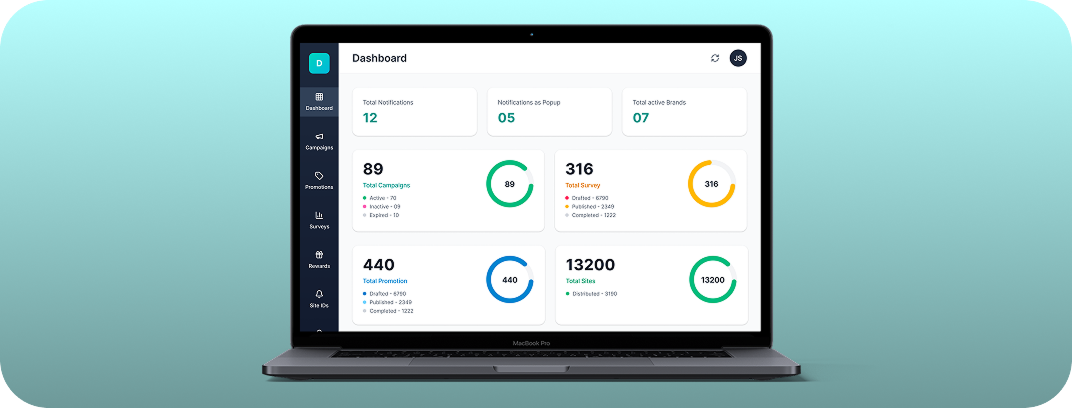
Complete RegTech & Compliance Automation Solutions for Financial Enterprises
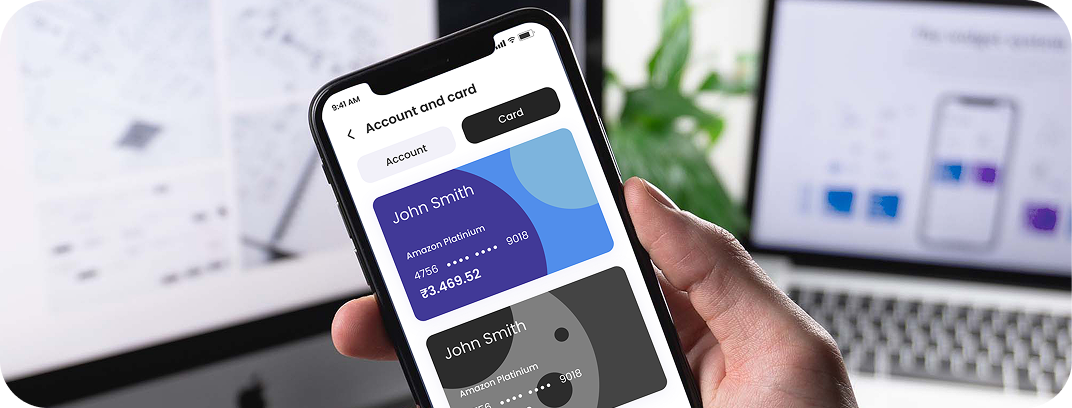
KYC and AML Automation
Application Security (RASP)
Identity and Access Management
Fraud Detection and Monitoring
Regulatory Reporting & Compliance
TECHNICAL HIGHLIGHTS
Application Security (RASP) by People Who Have Delivered 1000+ Projects
Real-Time Threat Intelligence
Hardware-Level Device Identity
Code Integrity & Anti-Tamper Protection
Immutable Compliance Auditing
Resource-Optimized Security Engine

Featured content
Our Latest Thinking in RegTech & Compliance Automation

May 22, 2026
AI in Insurance: Building Production-Ready Products for Claims, Underwriting, and Customer Experience
This blog breaks down what it takes to build production-ready AI in insurance across claims, underwriting, and customer experience. It covers the gap between AI pilots and live deployments, the architecture and governance requirements that determine whether a system holds up at scale, and what insurers need to get right across data infrastructure, compliance, and human oversight before going live.

May 22, 2026
Building AI Investment Platforms: From Predictive Analytics to Personalized Portfolio Insights
A technical and strategic guide for product and engineering leaders on building AI investment platforms, from data infrastructure and compliance to personalization and development costs.
May 18, 2026
Your Vibe Code Has No Memory. DESIGN.md Fixes That.
A single Markdown file called DESIGN.md gives your AI agent the design memory it lacks — keeping your UI consistent across every session.

May 15, 2026
Build vs Buy: Choosing the Right AI Strategy for Insurance Companies
Build or buy AI for insurance? Learn how to avoid vendor lock-in, lower AI operating costs, and build scalable, compliant insurance platforms.

May 14, 2026
Building a Production-Ready Image Cropper in React Native
A practical guide to building a custom gesture-driven image cropper in React Native, with support for both profile and cover photo crops.

Apr 23, 2026
From Manual Testing to AI-Assisted Automation with Playwright Agents
This blog discusses the value of Playwright Agents in automating workflows. It provides a detailed description of setting up the system, as well as a breakdown of the Playwright Agent’s automation process.
Build with us.Accelerate your Growth.
Customized solutions and strategiesFaster-than-market project deliveryEnd-to-end digital transformation services
Trusted By
Book a Discovery Call
Build with us.Accelerate your Growth.
- Customized solutions and strategies
- Faster-than-market project delivery
- End-to-end digital transformation services
Trusted By

What You Need to Know